|
1 ˵��
�������������ص�ַ
CentOS 5.2-----------------------------------------------------���ȶ���Linux������
ppp-2.4.3.tar.gz-----------------------------------------------PPP������
openssl-0.9.8i.tar.gz-----------------------------------------����֤���������
xl2tpd-1.2.3.tar.gz--------------------------------------------FreeRadius������������
openswan-2.6.19.tar.gz-------------------------------------IPSec������
1.2 ʵ�ֹ��̼���������
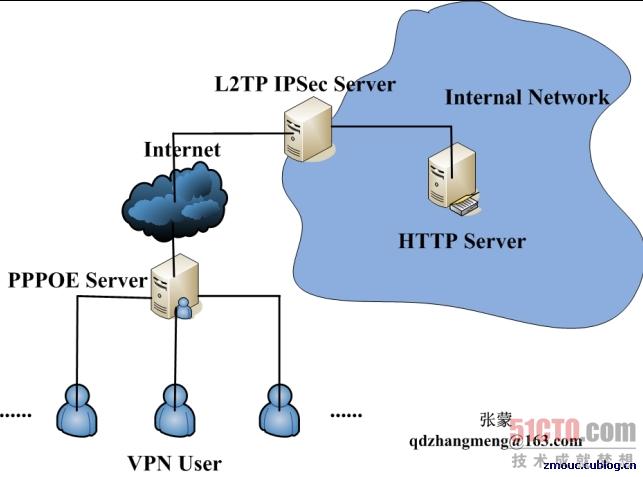
���ǵ�����������������ͼ��ʾ��
���Dz���VM��������飬VM�е�������������:
��VMware�ṩ��Virtual Network Editor�е�“Host Virtual Network Mapping”ѡ��У���VMNet2��ΪNot bridged������ұߵ�“>”��ť��subnet��IP��ַ����172.16.1.0��ȷ����
VPNGateway�������Ҫ������һ������,Ȼ����Linux�°����±����ø������������������������ѡ��������Ӧ�����硣����VPNGateway������0����VMNet0������1����VMNet2������1��Ĭ��������Ϊ192.168.2.1��
���⣬XP�����Զ�λ��VMNet0������Ҫ�������á�
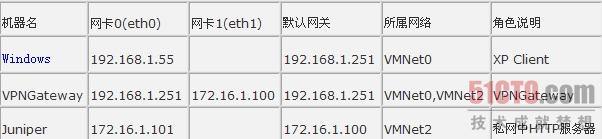
���У�192.168.1.0/24����ģ��������windows xpģ���������ŵ�VPN�ͻ�����
172.16.1.0/24����ģ��������JuniperΪ������һ̨��������Ϊ��ҵ�ڲ���HTTP��������
#P#
2.���������
������̲���������������ļ����£�
|
OpenSWan ��Ҫ�����ļ���
/etc/ipsec.secrets ��������private RSA keys �� preshared secrets (PSKs)
/etc/ipsec.conf �����ļ�(settings, options, defaults, connections)
OpenSWan ��Ҫ����Ŀ¼ ��
/etc/ipsec.d/cacerts ���X.509 ��֤֤�飨��֤�飭"root certificates"��
/etc/ipsec.d/certs ���X.509 �ͻ���֤�飨X.509 client Certificates��
/etc/ipsec.d/private ���X.509 ��֤˽Կ��X.509 Certificate private keys��
/etc/ipsec.d/crls ���X.509 ֤�鳷���б���X.509 Certificate Revocation Lists��
/etc/ipsec.d/ocspcerts ���X.500 OCSP ֤�飨Online Certificate Status Protocol certificates��
/etc/ipsec.d/passwd XAUTH �����ļ���XAUTH password file��
/etc/ipsec.d/policies ���Opportunistic Encryption �����飨The Opportunistic Encryption policy groups��
|
|
[root@mm ~]# cat /etc/ppp/chap-secrets # Secrets for authentication using CHAP #
client server secret IP addresses
test1 * test1 *
l2tptest1 * l2tptest1 10.1.1.1
l2tptest2 * l2tptest2 *
|
|
[root@mm ~]# cat /etc/ipsec.secrets
RSA /etc/ipsec.d/private/vpngateway.key "123456"
#192.168.1.251 %any : PSK "123456"
|
|
[root@mm ~]# cat /etc/ipsec.conf
#version 2.0
config setup
interfaces=%defaultroute
nat_traversal=yes
virtual_private=%v4:192.168.0.0/16,%v4:10.0.0.0/8,%v4:172.16.1.0/24,%v4:!192.168.1.0/24
conn %default
compress=yes
authby=rsasig
leftrsasigkey=%cert
rightrsasigkey=%cert
#conn roadwarrior
#left=172.16.1.100
#leftcert=vpngateway.cert
#leftsubnet=172.16.1.0/24
#right=%any
#auto=add
conn l2tpx509
pfs=no auto=add
left=192.168.1.251
leftcert=vpngateway.cert
leftprotoport=17/1701
right=%any
rightca=%same
rightprotoport=17/%any ############################################################################# #configure preshared secret authentication
#conn l2tp
# authby=secret
# pfs=no
# auto=add
# type=transport
# left=192.168.1.251
# leftprotoport=17/1701
# right=%any
# rightprotoport=17/%any ############################################################################# #include /etc/ipsec.d/examples/no_oe.conf
|
|
[root@mm ~]# cat /etc/ppp/options.xl2tpd
ipcp-accept-local
ipcp-accept-remote
ms-dns 192.168.10.1
ms-dns 192.168.10.3
ms-wins 192.168.10.2
ms-wins 192.168.10.4
#noccp
auth
crtscts
idle 1800
mtu 1410
mru 1410
nodefaultroute
debug
lock
proxyarp
connect-delay 5000
logfile /var/log/l2tpd.log
proxyarp
|
|
[root@mm ~]# cat /etc/xl2tpd/xl2tpd.conf
[global]
listen-addr = 192.168.1.251
port = 1701
auth file = /etc/ppp/chap-secrets
debug tunnel = yes
[lns default]
ip range = 172.16.1.10-172.16.1.254
local ip = 192.168.1.251
require chap = yes
refuse pap = yes
require authentication = yes
name = mm's L2TP VPN Server
ppp debug = yes
pppoptfile = /etc/ppp/options.xl2tpd
length bit = yes
|
|
����֤�飨�ڻ���֮�临��֤����ȷ����ȫ�ԣ���
#cp cacert.pem /etc/ipsec.d/cacerts
#cp vpngateway.cert /etc/ipsec.d/certs
#cp vpngateway.key /etc/ipsec.d/private
#cp crl.pem /etc/ipsec.d/crls/
|
|
CA����Ŀ¼�� /root/CA
# openssl req �\x509 �\days 3650 �\newkey rsa:1024 �\keyout cakey.pem �\out cacert.pem
# mkdir newcerts
# touch index.txt
# echo "01" > serial
# echo "01" > crlnumber
# mkdir private
# cp cakey.pem ./private/
# openssl ca �\gencrl �\out crl.pem
# openssl req �\newkey rsa:1024 �\keyout vpngateway.key �\out vpngatewayreq.pem
# openssl ca �\in ../vpngatewayreq.pem �\days 365 �\out ../vpngateway.cert �\notext
# openssl pkcs12 �\export �\in cacert.pem �\inkey cakey.pem �\out demoCA.p12
�������windows��˽Կ��֤�飺
# openssl req �\newkey rsa:1024 �\keyout windows.key �\out windowsreq.pem
# openssl ca �\in ../windowsreq.pem �\days 3650 �\out ../windows.cert �\notext
# openssl pkcs12 �\export �\in windows.cert �\inkey windows.key �\out windows.p12
ע�⣬�ڵ���P12�ļ�ʱ�������ȡCA��Կ�����룬Ȼ����ָ������p12�ļ��е�֤����Ҫ
�����룬�����ж���ȷ�ϡ�
|
#P#
�û���l2tptest1������l2tptest1�����в��ţ�
���Կ�����õ�IP ��/etc/ppp/chap�\secrets �ļ���ָ�����Ǹ�IP��

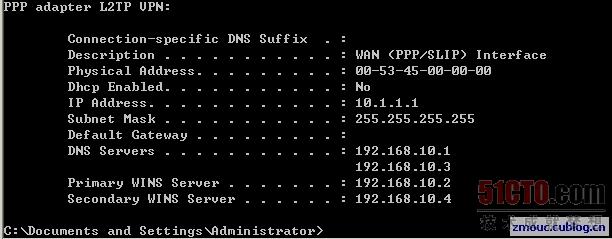
�û���l2tptest2������l2tptest2�����в��ţ�
���Կ�����õ�IP �Ǵӵ�ַ���л�õģ�
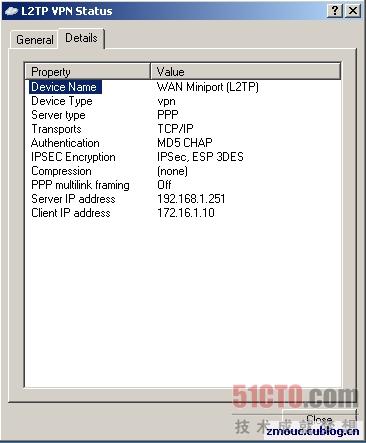
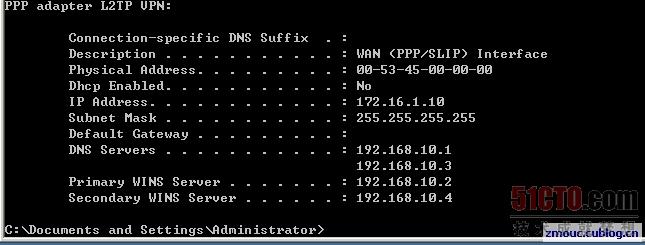
һ�������IJ���������Ϣ���£�
|
xl2tpd[7581]: build_fdset: closing down tunnel 34285
xl2tpd[7581]: get_call: allocating new tunnel for host 192.168.1.55, port 1701.
xl2tpd[7581]: get_call: allocating new tunnel for host 192.168.1.55, port 1701.
xl2tpd[7581]: control_finish: Peer requested tunnel 3 twice, ignoring second one.
xl2tpd[7581]: build_fdset: closing down tunnel 46042
xl2tpd[7581]: Connection established to 192.168.1.55, 1701. Local: 26849, Remote: 3 (ref=0/0).
LNS session is 'default'
xl2tpd[7581]: start_pppd: I'm running:
xl2tpd[7581]: "/usr/sbin/pppd"
xl2tpd[7581]: "passive"
xl2tpd[7581]: "�\detach"
xl2tpd[7581]: "192.168.1.251:172.16.1.10"
xl2tpd[7581]: "refuse�\pap"
xl2tpd[7581]: "auth"
xl2tpd[7581]: "require�\chap"
xl2tpd[7581]: "name"
xl2tpd[7581]: "mm's L2TP VPN Server"
xl2tpd[7581]: "debug"
xl2tpd[7581]: "file"
xl2tpd[7581]: "/etc/ppp/options.xl2tpd"
xl2tpd[7581]: "/dev/pts/1"
xl2tpd[7581]: Call established with 192.168.1.55, Local: 64654, Remote: 1, Serial: 0
xl2tpd[7581]: network_thread: select timeout
xl2tpd[7581]: network_thread: select timeout
xl2tpd[7581]: child_handler : pppd exited for call 1 with code 10
xl2tpd[7581]: call_close: Call 64654 to 192.168.1.55 disconnected
xl2tpd[7581]: control_finish: Connection closed to 192.168.1.55, port 1701 (), Local: 26849,
Remote: 3
xl2tpd[7581]: build_fdset: closing down tunnel 26849
xl2tpd[7581]: Trustingly terminating pppd: sending TERM signal to pid 7633
xl2tpd[7581]: pppd 7633 successfully terminated
|
����L2TP IPSec VPN �������ļ��裬����ѧϰ��������л��кܶ�ϸ����Ҫѧϰ����Ϥ���д���һ�����о���
|

